Image Clarification: Not a Bar to Admissibility
One of the most commonly litigated issues regarding digital image evidence is the propriety of and limits to image clarification. Parties who tender clarified images argue that the clarified images allow the viewer to see more detail in the images while the opposing party urges the court to rule the images inadmissible on...

Image Accuracy: Why the Correct Aspect Ratio Matters
Part of the process of authenticating a video image is to show that the image is an accurate depiction of what the camera recorded. One important technical issue bearing upon image accuracy that must be considered is aspect ratio (the height to width ratio of the image). It is not uncommon to see...
Preparing for Trial: Meetings with Attorneys
Pre-trial meetings with the attorney who will be presenting the expert’s evidence in court are not a luxury. They are essential. Though it may be at times challenging to arrange, it is recommended that the expert insist on a meeting. Every time I have a case that involves expert evidence, I have at...
Expert Witnesses: The Need to Remain Current
Expert witnesses are professionally and ethically obligated to remain current in their field of expertise. Parties who retain experts and the courts that rely upon their testimony are entitled to expect that they are receiving the latest information from their experts. When I am tendering an expert witness before the court, in the...
What Should be in an Expert Report?
The culmination of an expert’s work is the expert report. The expert report represents the final written product of the expert and serves a number of important purposes. First, it documents the methodology and work of the expert, thereby outlining for counsel what work the expert has undertaken, what processes were used and...
Social Media Images: Authentication Challenges
The widespread use of handheld cameras and the penchant for posting video to social media have created significant evidentiary challenges from an authentication perspective. For example, cameras mounted on motorcycles that are driven in a highly dangerous manner occasionally result in the posting of such videos to a social media site, ostensibly for...
Using Digital Signatures to Authenticate Video Images
Watermarks were discussed in an earlier post as a method of authenticating video images or showing that image alteration has occurred. Watermarks come with limitations. A more commonly used method for authenticating digital images is the use of digital signatures whereby digital signatures are generated in an authentication system and stored on a...

Using Watermarks to Authenticate Video Images
Another method of authenticating video images is to show scientifically that an image has not been altered or conversely that alteration has occurred. One such method has been the use of watermarking which modifies the digital video content by the superimposition of a watermark. As Erik Berg noted:[i] Digital watermarks are generally used...
Authentication and the Use of Audit Trails
In order for video evidence to be admitted at trial, the tendering party must prove that the images are authentic. There are a number of technical approaches that are available to assist with video authentication. This post will address the use of audit trails as part of the process of establishing authentication. Proper...
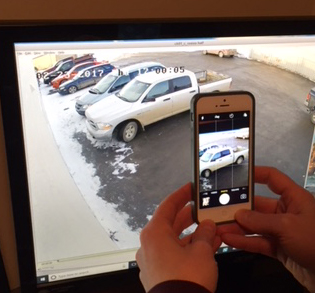
Authenticating Monitor Photographs
The proper method of presenting surveillance video evidence at trial is to show all relevant authenticated images that have been exported from the DVR or server. Occasionally, the only evidence of the original video that exists is photographs taken of the video monitor at the surveillance location. This less than ideal situation can...