Authentication of Social Media and Other Videos in Northern Ireland Terrorism Cases
Courts in Northern Ireland have made important admissibility rulings regarding the authentication of videos presented as evidence in terrorism cases. One case addresses the admission of key video evidence when no authentication witnesses were called at all while the second case deals with the admissibility of unsupported video as well as questionable video posted...

Case Study: How a YouTube Rap Video was Used to Convict a Defendant
Video uploaded to social media sites must be authenticated in order to be admissible. The question of what level of proof is required to meet the authentication requirement was explored recently in United States v. Pettway, 2018 WL 4958962 (United States District Court, W.D. New York). The defendant was convicted by a jury of various...

Case Study: Authenticating Facebook Video – “We Live!”
The admissibility of Facebook video was at issue in Lamb v. State of Florida, 246 So.3d 400 (2018) (District Court of Appeal of Florida, Fourth District). The defendant was being tried for two carjackings and the state sought to introduce Facebook Live video apparently recorded within minutes of the carjackings and purporting to show the...
Case Study: Failure to Authenticate Surveillance Video Leads to Exclusion of Evidence
Authentication is a prerequisite for the admissibility of video evidence. As discussed in several articles on this website, failure by the tendering party to lead sufficient reliable evidence to prove authentication will result in a ruling of inadmissibility. Such was the case in the May 21, 2018 ruling in State of New York v....

Image Accuracy: Why the Correct Aspect Ratio Matters
Part of the process of authenticating a video image is to show that the image is an accurate depiction of what the camera recorded. One important technical issue bearing upon image accuracy that must be considered is aspect ratio (the height to width ratio of the image). It is not uncommon to see...
Social Media Images: Authentication Challenges
The widespread use of handheld cameras and the penchant for posting video to social media have created significant evidentiary challenges from an authentication perspective. For example, cameras mounted on motorcycles that are driven in a highly dangerous manner occasionally result in the posting of such videos to a social media site, ostensibly for...
Using Digital Signatures to Authenticate Video Images
Watermarks were discussed in an earlier post as a method of authenticating video images or showing that image alteration has occurred. Watermarks come with limitations. A more commonly used method for authenticating digital images is the use of digital signatures whereby digital signatures are generated in an authentication system and stored on a...

Using Watermarks to Authenticate Video Images
Another method of authenticating video images is to show scientifically that an image has not been altered or conversely that alteration has occurred. One such method has been the use of watermarking which modifies the digital video content by the superimposition of a watermark. As Erik Berg noted:[i] Digital watermarks are generally used...
Authentication and the Use of Audit Trails
In order for video evidence to be admitted at trial, the tendering party must prove that the images are authentic. There are a number of technical approaches that are available to assist with video authentication. This post will address the use of audit trails as part of the process of establishing authentication. Proper...
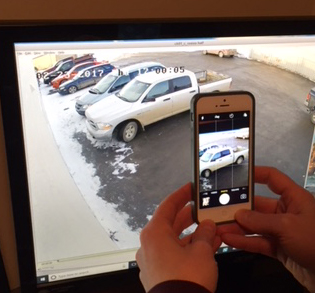
Authenticating Monitor Photographs
The proper method of presenting surveillance video evidence at trial is to show all relevant authenticated images that have been exported from the DVR or server. Occasionally, the only evidence of the original video that exists is photographs taken of the video monitor at the surveillance location. This less than ideal situation can...